
The Internet is extensively used to exchange information across borders which has resulted in the collection of large data sets. The information collected by the organizations from customers, vendors, and distributors, and the information exchanged across the organization on one hand, plays an integral role in the success of the organization if maintained properly as these data sets help organizations to take appropriate action. On the other hand, if the gathered data is not secured it may result in the risk of financial loss, disruption in the operations, and damage to the company’s reputation. These risks have pushed the security management of the organizations to secure the data management system and prevent hackers from hacking the organization's data. Therefore, to protect the data of employees, customers, vendors, distributors, and of all the people associated with the company, the organizations should develop a security system that supports the protection of data despite the location in which the system is operated. To date, various techniques which include artificial intelligence, blockchain, machine learning, and deep learning models are widely used to secure systems worldwide.
 Despite the high technicalities and the advanced security the management system used by the organizations to protect the data, the information system of the organization
may still be hacked because of loops and a lack of knowledge of the employees about malicious software. The practices that threaten information security including leaving the devices unattended in public places, leaving their computers and systems
unlocked, and employees who fail to comply with the company policy.
Despite the high technicalities and the advanced security the management system used by the organizations to protect the data, the information system of the organization
may still be hacked because of loops and a lack of knowledge of the employees about malicious software. The practices that threaten information security including leaving the devices unattended in public places, leaving their computers and systems
unlocked, and employees who fail to comply with the company policy.
Therefore, to protect the data of employees, customers, vendors, distributors, and of all the people associated with the company, the organizations should develop a security system that supports the protection of data despite of the location in which the system is operated. To date, various techniques which include artificial intelligence, blockchain, and machine learning and deep learning models are widely used to secure the systems worldwide.

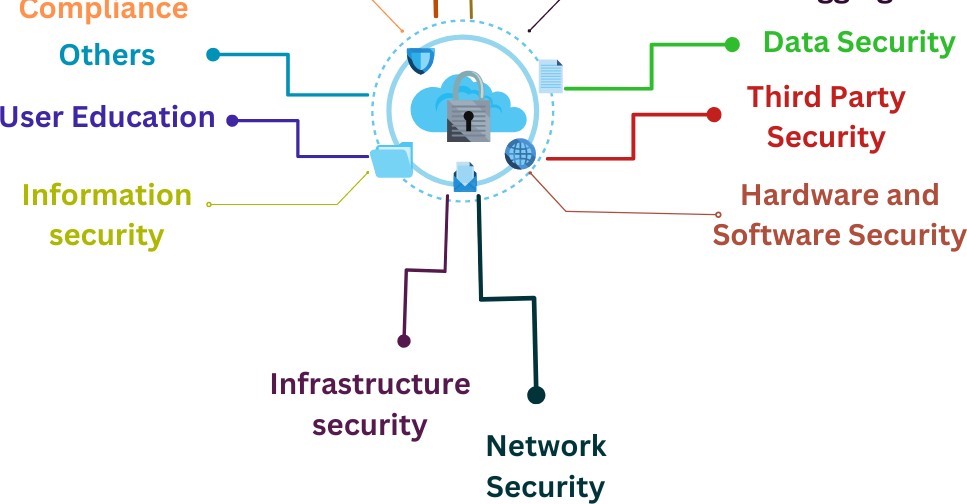
Following are the types of cybersecurity that an organization can apply to secure the information,
Execute intricate codes to protect the data so that it becomes dimcult for the hacker to access the data.
Protects and encrypts the data so that unauthorized users cannot access the information of the organization.
This security measure protects the power networks and data centers that form the infrastructure.
Uses tools such as remote access management, two-factor authentication, and practical firewall, and rules and configiuration to protect networks from invasion while accessing the applications in cloud.
This type of cyber security focuses on the information provided to the employees and all the workers regarding the threats of cyber security.
This type of cyber security gives access to individual users to ensure that only the right person have access to right resources.
Hardware and Software security ensures physical security through biometric access, scans, audits and patches & server hardening.
Manages the vulnerabilities and attacks, monitors tramc, manages logs, and provides strategies to mitigate the risk.
It secures the digital information throughout the data life cycle to protect it from corruption, theft, or unauthorized access.
Security controls to protect the information system such as ISO/IEC 27001, NIST 800–53 are some of the internationally accepted standard controls that are adopted according to the businesses. Besides these, there are Audit and Assessment requirement that need to be adhered to by the organizations in order to protect the data management system.
Third-party security is a set of practices, services, and technologies that can identify the risks and protect your organization from security threats associated with third-party which include vendors, distributors, etc.
Besides the above listed types of cybersecurity there are other types as well which include,
1- Service Security Management
2- Internet Security
3- Cloud Security
4- Endpoint Security







