 June/15/2023
June/15/2023
The evolution of technology has improved the living standards of people all over the world which is widely used to enhance the customer experience. Organizations all over the world as a result of globalization offers products and services to customers across the borders through the use of technology which is why the large data sets of the customers flow through network to data centers allowing organizations whether they are non-profit organizations or private companies, to make more accurate decision regarding the selection of product, service improvement, customer experience enhancement, problem detection and reaching out to the target audience etc. The data set transmission on one hand is quite beneficial for organizations but on the other hand it also imposes threats to the organizations in the form of cyber-attacks. For instance, the data collected by the organizations is sometimes very sensitive such as credit card number, postal address, sometimes professional details, and sometimes personal details flow over the internet and is used by multiple organizations for different purposes and because of less security of the data people hesitate in sharing personal information over internet which may negatively affect the revenue stream of the firms and may prevent organizations that contribute to social well-being from identifying the authentic case (Taleb, 2022).
Statistics regarding the resistance of Japanese in 2019 while sharing data over mobile devices show that only 47.3% shared information regarding their gender, only 29.6% shared their authentic names over the internet, and only 23.8% shared their email over the internet (Statista, 2021). Another study that included a result of 1,000 Americans revealed that only 31% of people were willing to share their home address in 2019, and only 61% were willing to share their email address (Forbes).
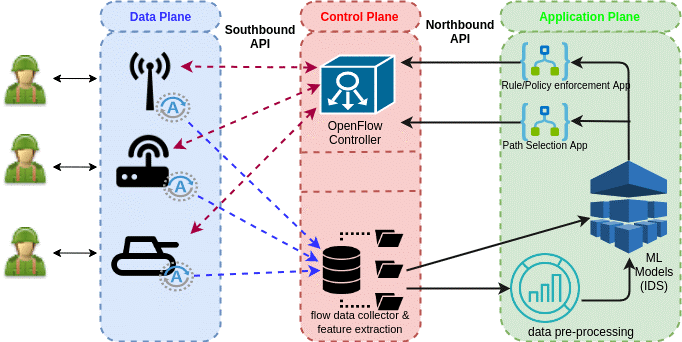
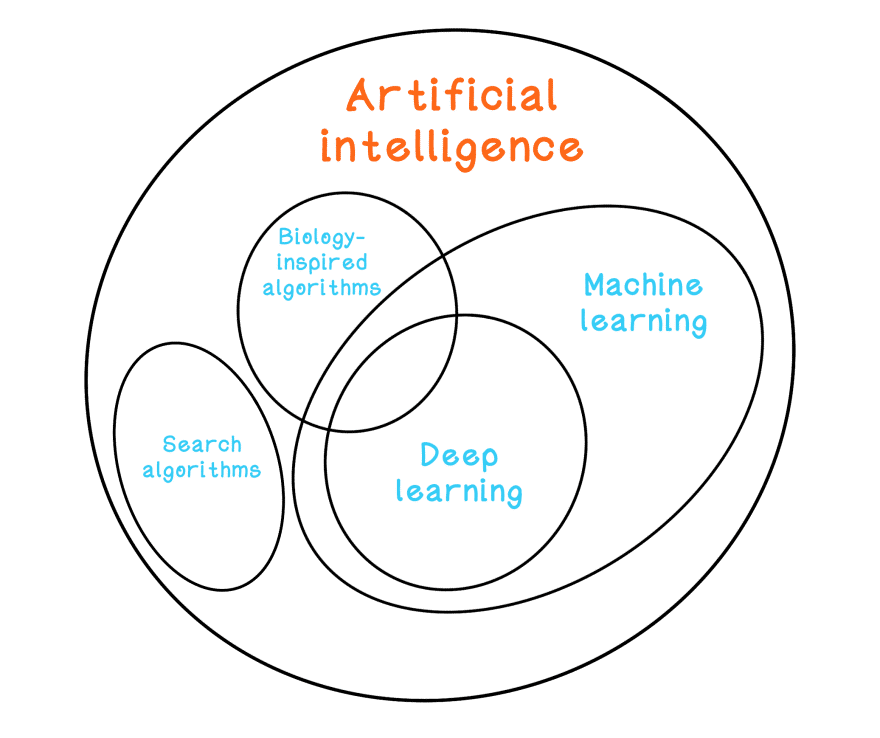
These threats however, can be reduced by using cyber threat intelligence (CTI) which without any intervention from human take appropriate preventive measures using cloud services through which it monitor the possible threats and can be implemented using an online threat sharing platform but CTI is considered as it is in the early stage (Taleb, 2022). Besides CTI, other techniques and Machine Learning models can be used to mitigate cyber-attacks which include deep learning model, rain forest, and K-NN. However, these AI based models may reflect high false-positive rates, and low true-positive rates in case of inappropriate modelling and for improved analysis of the threat a hybrid deep learning based model was proposed based on convolutional neural network (CNN) and quasi-recurrent neural network (QRNN). The CNN capture the change in space whereas QRNN represents time factor during the movement and by using this model organizations can improve the real time analysis in cyber threat intelligence. Besides CNN and QRNN, Restricted Boltzmann Machine and FFNN algorithm is also one method of reducing the cyber threat, this model deals with the cyber threat-distributed denial-of-service (DDoS) and has an accuracy of 97.5%. Other methods that deals with the information theft, reconnaissance, and DDos are J48, and FFNN (Ge, 2019). K-NN is another method that is 99% accurate and deals with DDoS, denial-of-service (DoS), data exfiltration, keylogging, OS fingerprinting, and service scan threat (Ullah, 2020). Other models with 90% or above 90% accuracy level include C5-SVM, Decision tree-RF, Recursive Bayesian estimation, FCNN, CNN, and LSTM, C4.5 (Lee, 2019), Multilayer perceptron (MLP), SVM, and linear discriminant analysis (LDA), Stacked auto-encoder (SAE), GWO-CNN, and CNN-LSTM. Through using these models appropriately organizations can improve the mechanism for securing the data and for preventing any cyber-attack which can also help the organizations to attract more individuals to their products or services through building trust.
1- Statista, 2021. Share of mobile device users who disclosed personal information on the internet in Japan as of December 2019, by type of information.
2- Forbes. People Are Becoming More Reluctant To Share Personal Data, Survey Reveals.
3- Taleb, N.A., Saqib, N.A., 2022. Towards a Hybrid Machine Learning Model for Intelligent Cyber Threat Identification in Smart City Environments.



